Automotive Telematics Systems
Automotive Telematic Systems
The telematic systems send and receive the vehicle information and vehicle remote commands to and from user over the telecommunication (GSM, 4G/LTE/3G/2G). The telematic system connects the Vehicle to OEM, Dealer, Service station and Driver/Owner, this connectivity can be explored for many use cases (e.g. Insurance, Warranty, Maintenance, Shared Mobility).The following telematic systems changing the future of modern vehicles
Vehicle tracking system
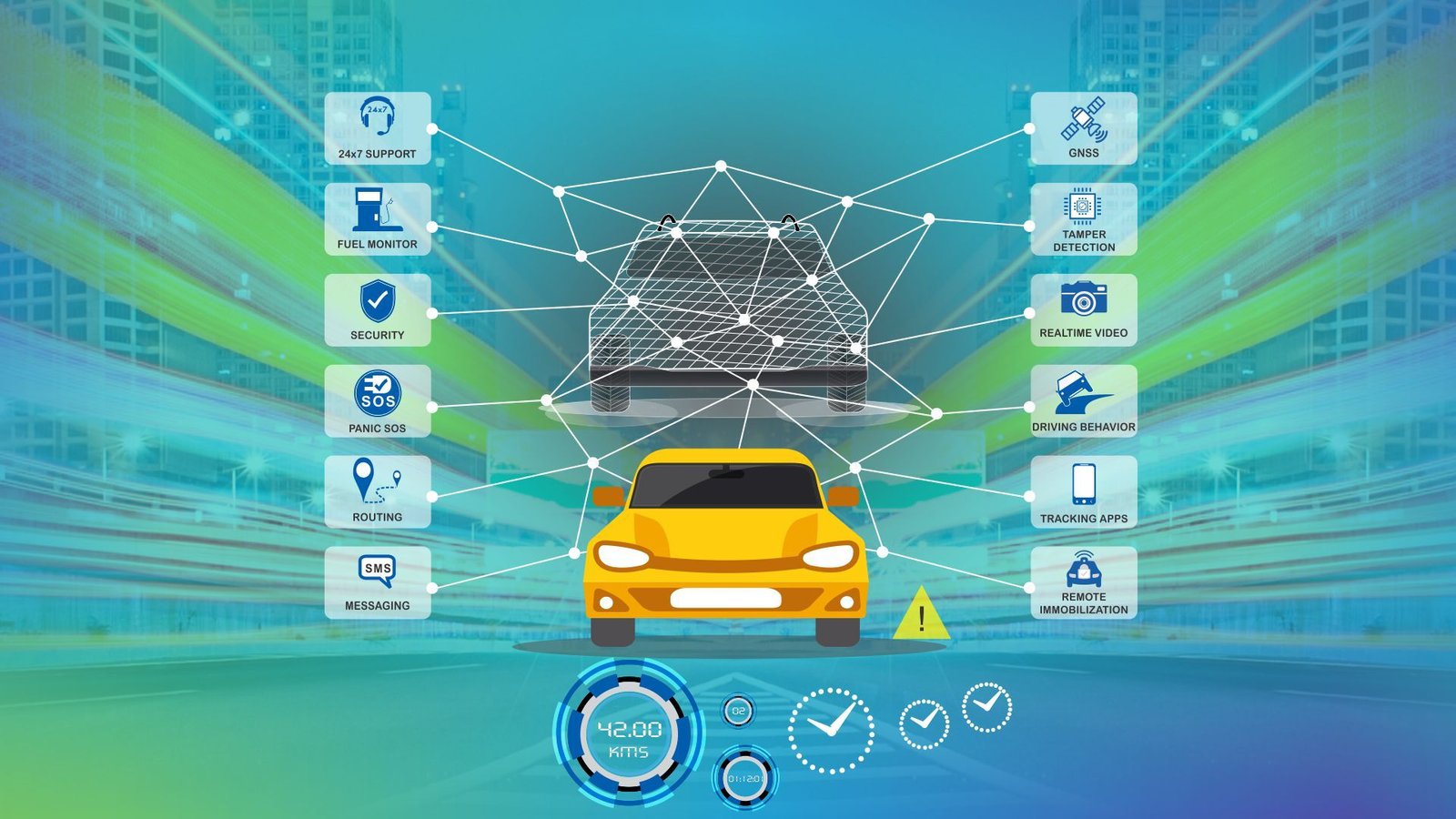
The vehicle tracking systems sends important vehicle information and alerts to cloud, this information can be used for fleet management, asset tracking, driver behavior monitoring and vehicle usage monitoring. The OEMs can use the information for warranty checks.
Following are the key features of Vehicle tracking system:
Shared Mobility:
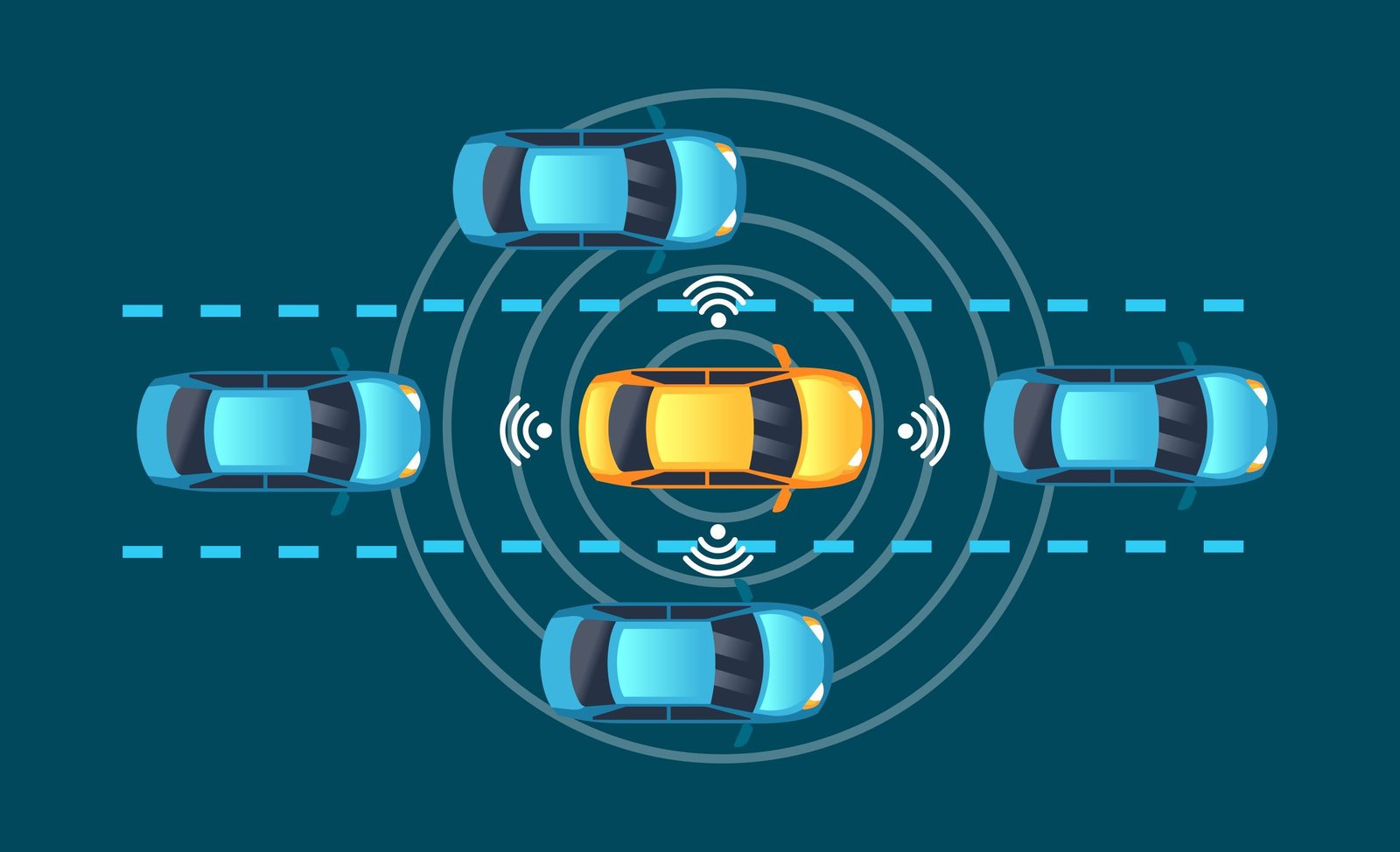
Shared mobility is changing the mode of transportation and commuting. Instead individual own a vehicle, now the trend changed to share and use a vehicle. Shared mobility is changing the people lifestyle and helping in reduce the carbon footprint. The following types of shared mobility are in the current world
The telematics are helping in track, schedule, maintain and manage the vehicles in shared mobility efficiently.
Online vehicle diagnostics/Predictive maintenance
Telematic system collects the vehicle health status, important parameters(RPM, Odometer, Engine hours, Total hours, Fuel level/Battery discharge indicator, Brake POT, Throttle POT), diagnostic trouble codes (DTCs) from sensors, actuators and other ECUs ( E.g. Engine control unit ) and upload the data to cloud.
The data in the cloud processed by automated software which does continuous predictive analysis and sends maintenance alerts to OEM, Dealer and Owner/Driver. The alerts can be sent in an Email, SMS or mobile app notification. This increases the vehicle safety and reduces breakdowns and vehicle maintenance cost.

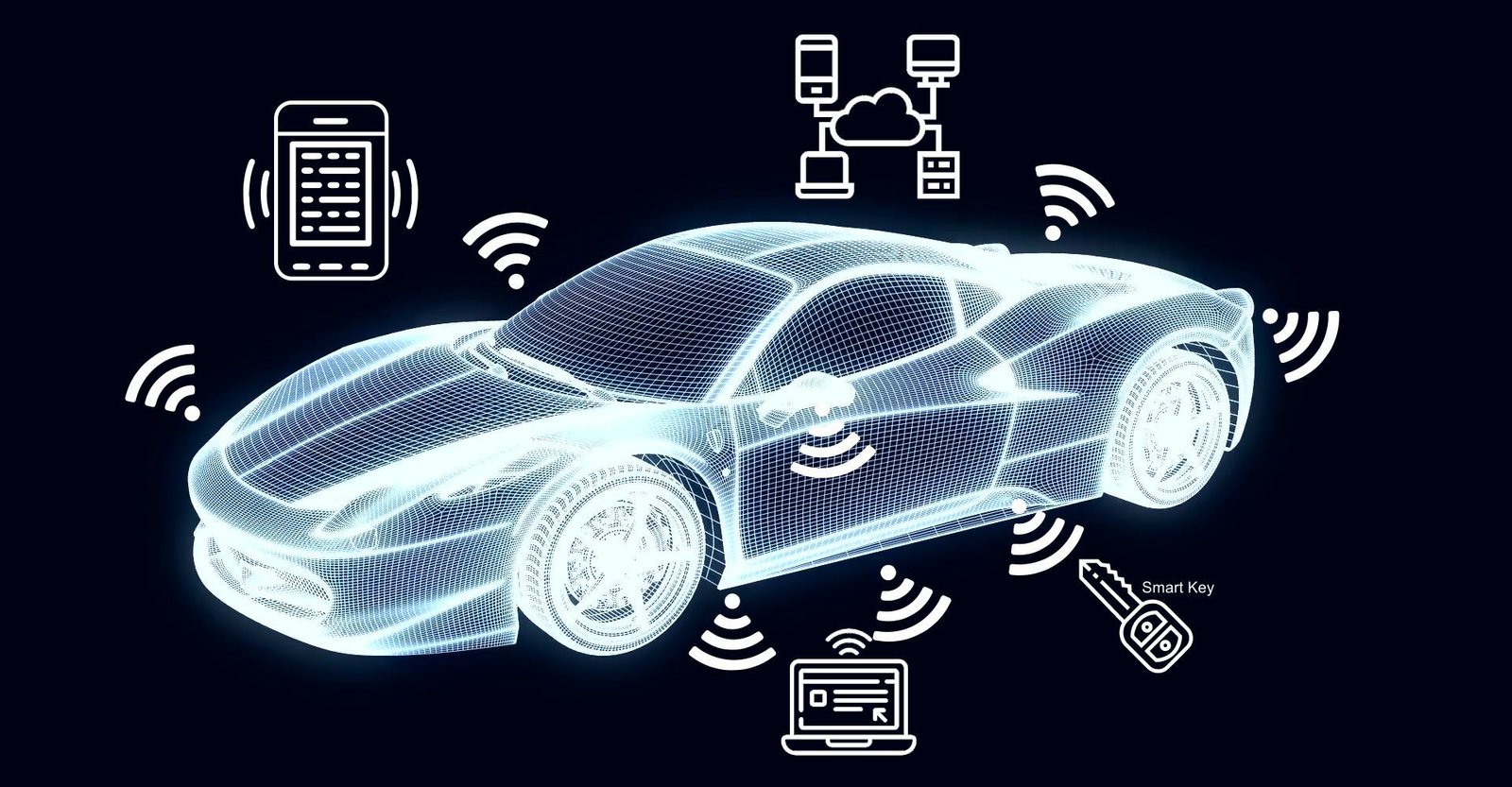
Remote control operations
User can remote control the engine on/off (Immobilizer), Lights, Mirrors, Doors, Roof top and Trailers via internet, Radio Frequency (E.g. Bluetooth). Immobilizer unit is very useful in protect vehicle from theft, and it is useful in control the vehicle engine on/off in Self Driving vehicles.
Secure over the air upgrades (COTA and FOTA)
In olden days, upgrading software in vehicle requires either, technician has to visit vehicle site, or the vehicle has to be brought to Service center, this involves a lot of efforts and cost. Now, with connected telematic gateway systems, upgrade a system in the vehicle is very easy.
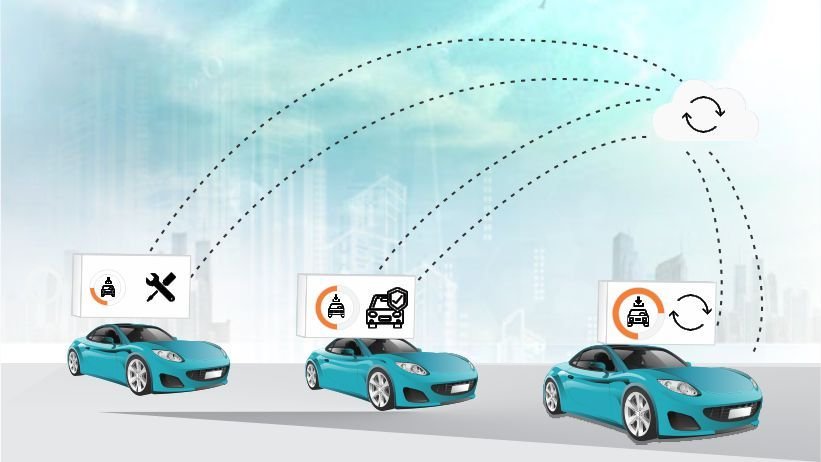
Telematic gateway system is an interface between Cloud and Vehicle. Any system that is connected to the in-vehicle telematic gateway unit can be upgrade with new configuration and firmware (software) over the air. User can select a system for upgrade in mobile/web application; the request reaches to gateway via Cloud, the telematic gateway pools the data in background and performs the actual upgrade operation in vehicle safe condition e.g. Vehicle stopped. To keep the Delta firmware upgrade over the air (DFOTA) is latest technique that reduces data usage and upgrade time. As part of DFOTA technique, the new ECU firmware file shall be compared with previously loaded firmware file and the differences captured in DFOTA file. The FOTA server sends the DFOTA file instead of original new firmware file to Telematic gateway system for the ECU upgrade.
Telematic gateway system is an interface between Cloud and Vehicle. Any system that is connected to the in-vehicle telematic gateway unit can be upgrade with new configuration and firmware (software) over the air. User can select a system for upgrade in mobile/web application, the request reaches to gateway via Cloud, the telematic gateway pools the data in background and perform the actual upgrade operation in vehicle safe condition e.g. Vehicle stopped. To keep the Delta firmware upgrade over the air (DFOTA) is latest technique that reduces data usage and upgrade time. As part of DFOTA technique, the new ECU firmware file shall be compared with previously loaded firmware file and the differences captured in DFOTA file. The FOTA server sends the DFOTA file instead of original new firmware file to Telematic gateway system for the ECU upgrade.

Infotainment
In-vehicle infotainment system provides entertainment and vehicle important information to the driver and co-passengers. Modern vehicles are integrating new technologies (Cloud, Web, Bluetooth, Wi-Fi, GSM, GNSS, Sensors) into infotainment for better connectivity and user experience.
The infotainment system fetches important vehicle parameters (RPM, Speed, Engine Hours, Odometer, Fuel level, Diagnostic Trouble Codes) from other ECUs and display on Dashboard display system.
- System Architecture
- ECU Software Architecture
- Telematic security
- ALTEN Global Technologies Services in BCM
- Case Study
Telematic System Architecture
ALTEN Global Technologies developed both Hardware and software (including server programs and mobile apps) for Vehicle tracking / Fleet management system, secure telematic gateway system and infotainment systems. This diagram shows basic architecture of telematic system
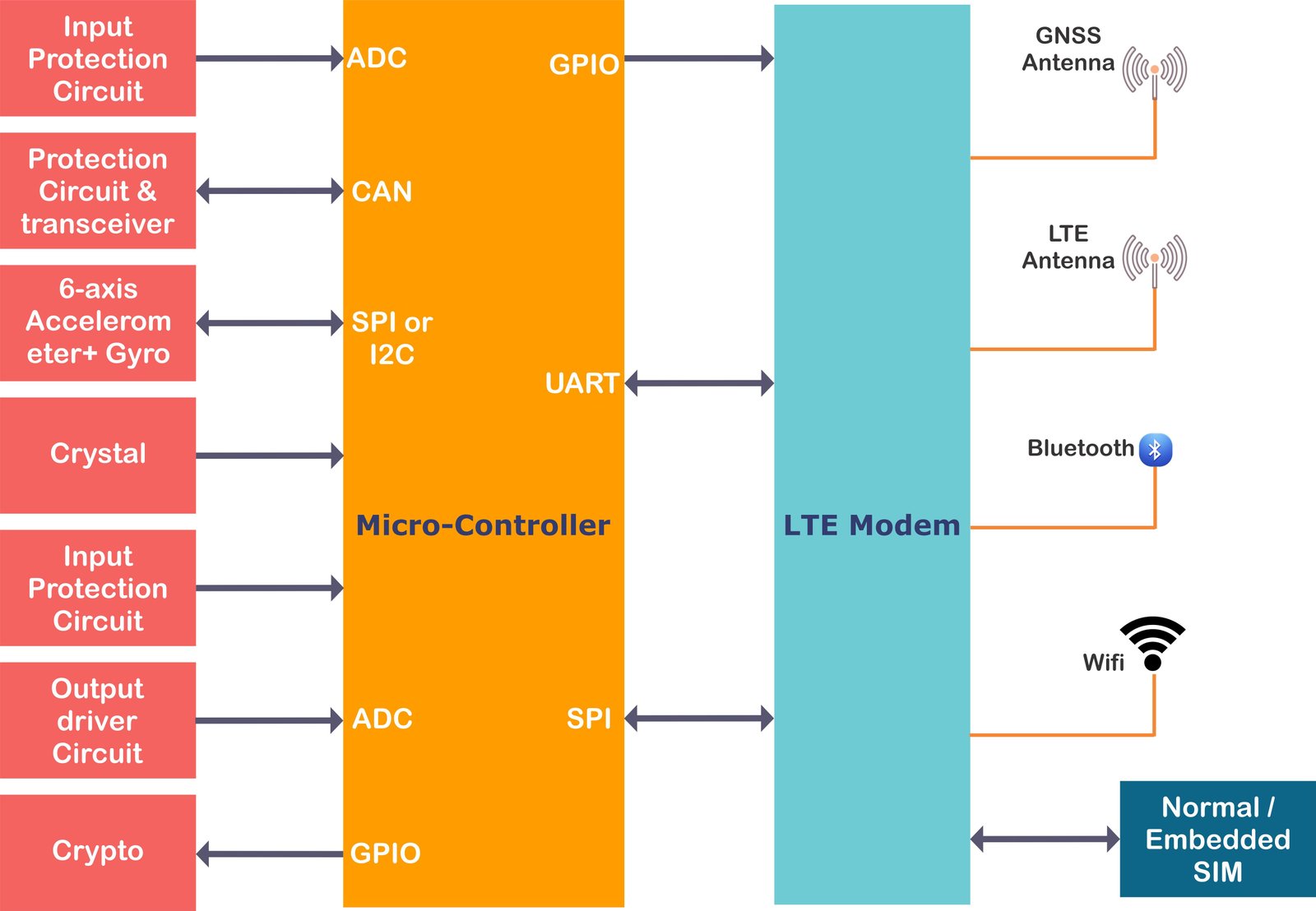
Key features of ALTEN Global Technologies developed telematic gateway ECU:
Key features of ALTEN Global Technologies Vehicle tracking ECU:
Key features of ALTEN Global Technologies Fleet management system (Mobile and Web application):
Telematic ECU Software Architecture
Security is the most important point telematic ECU architecture. Software developed to secure coding standards (e.g. CERT) and design guidelines (e.g. IEEE Center for Secure Design (CSD)) are less susceptible to security attacks. A few examples are below
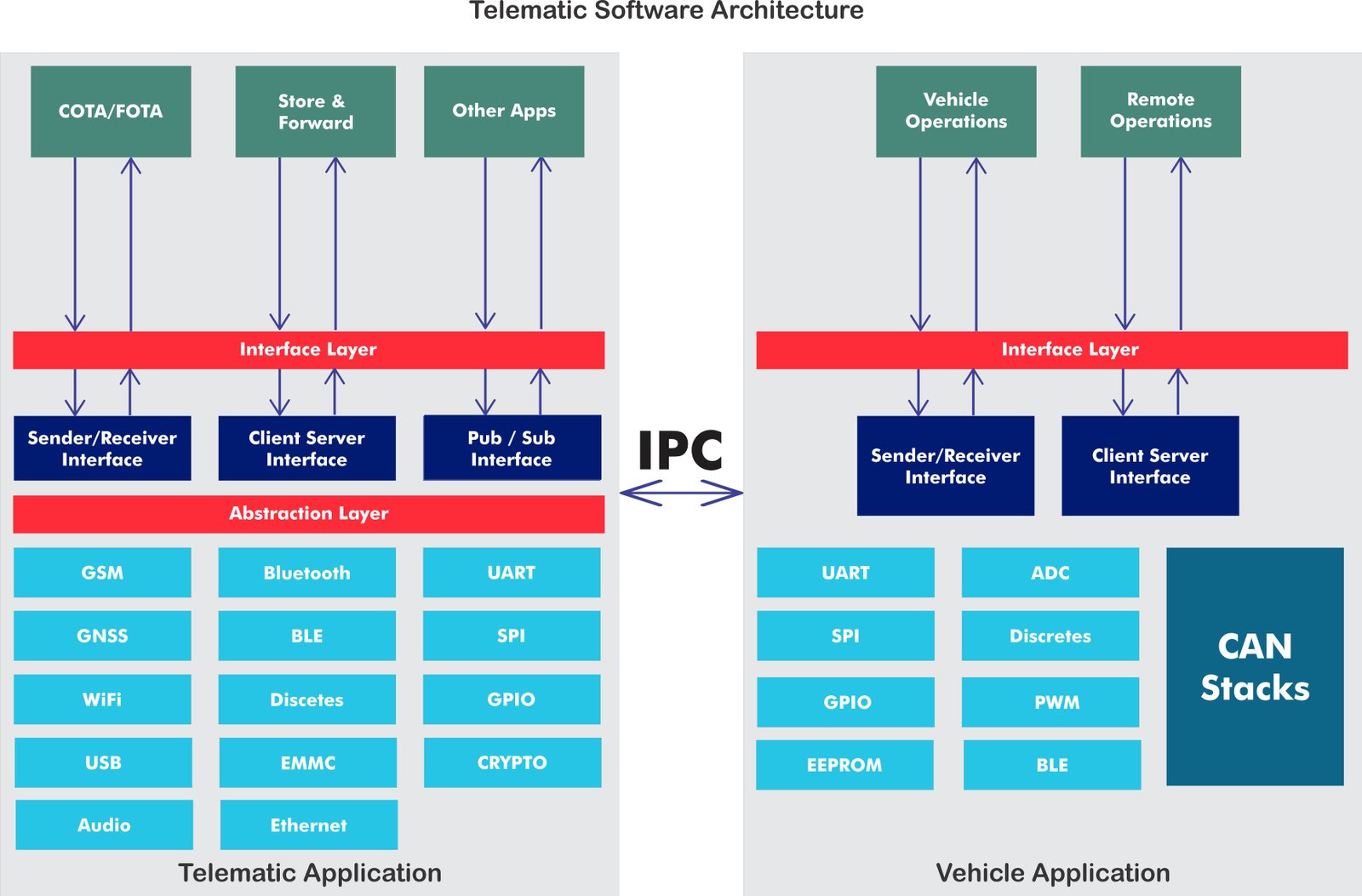
After security, the next import point is Store and Forward. When there is no network availability, the telematic system shall store the important information and forward the same information to Cloud upon the network availability.
Telematic ECU architecture shall be scalable for future updates. Telematic ECU undergo more frequent updates comparative to other ECUs, so the telematic ECU architecture shall support Firmware over the air upgrades.
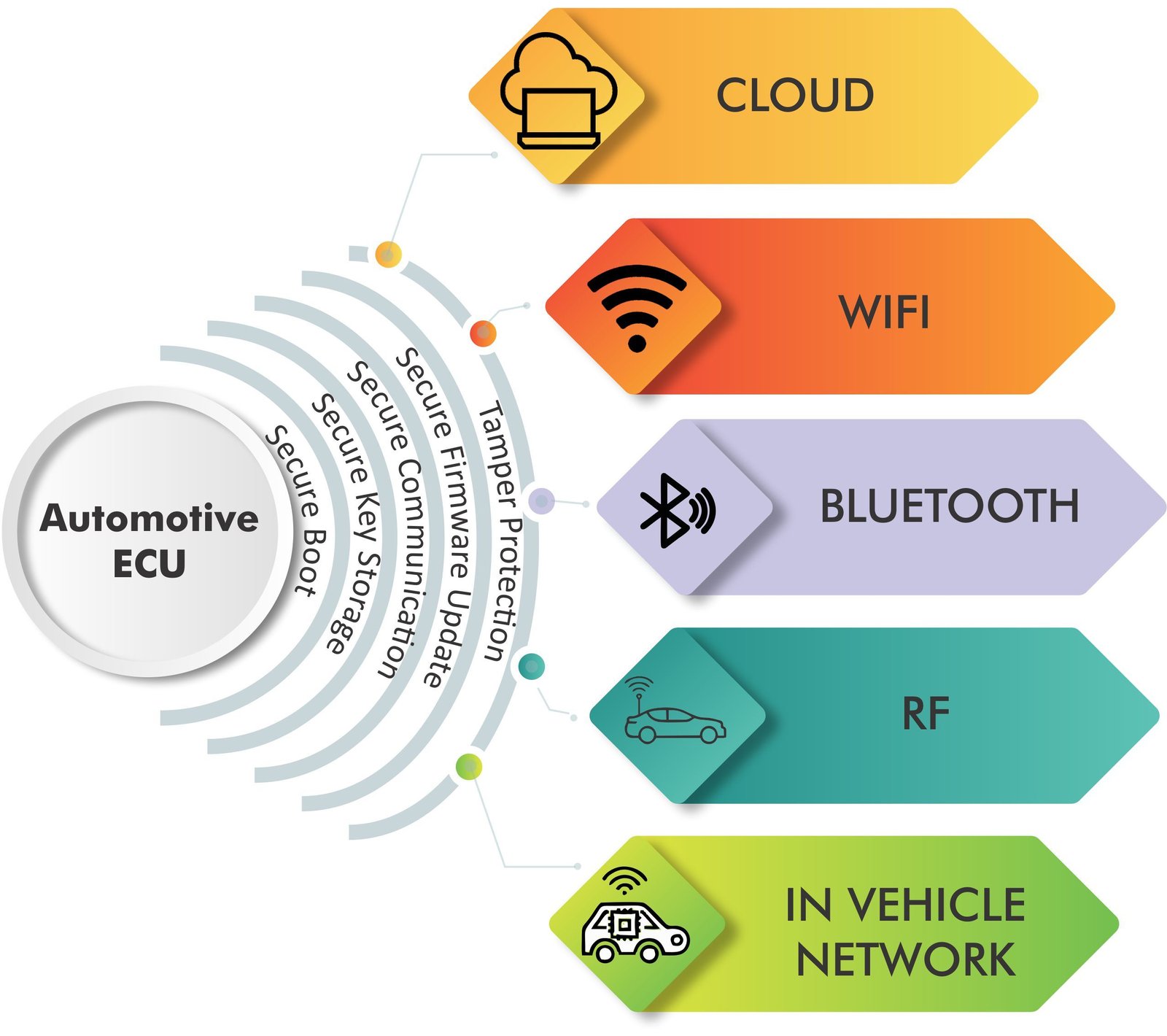
Telematic security
The telematic ECUs are equipped with the following hardware and software solutions to protect ECU from security attacks:
Hardware security protection
Software security protection
ALTEN Global Technologies Services in Telematics
ALTEN Global Technologies has very good experience in design and development of Telematic systems in Automotive domain. ALTEN Global Technologies has developed big scale telematic system to one of the leading OEM in India.
ALTEN Global Technologies is one stop solutions for entire Telematic echo system development. ALTEN Global Technologies provide services in design and develop full telematics echo system including Hardware, Software, Communication stacks, Security, Cloud micro services, Web applications, Mobile applications and Automatic test equipment.

1. THE CHALLENGE FACED BY CUSTOMER
Customer wants a solution which acts as a data logger and gateway. The solution is to be developed as Platform and the product will be derived from the platform, based on the business needs and requirements.
The challenges are
2. SCOPE OF WORK
ALTEN Global Technologies understood the customer’s requirements and the expected device functionality, by interacting with the customer’s technical teams. ALTEN Global Technologies came up with the below solutions:
2.1 SOLUTIONS AND SERVICES PROVIDED BY ALTEN Global Technologies
2.1.1 The Approach
ALTEN Global Technologies proposed two different hardware variants,